ATELIER COLOR Bauernhof Bastelbogen mit Tieren für Kinder zum Basteln ab 5+ Jahren Spielzeug aus Papier Bastelset Papiermodelle zum Spielen: Amazon.de: Spielzeug

Hühner aus Papptellern; Link führt leider nur zu einem Bastelbuch bei amazon, aber diese Hühner kri… | Basteln frühling ostern, Basteln ideen ostern, Bastelarbeiten

Holz Tiere Bauernhof 16-teilig, Bauernhoftiere zum Bemalen, Basteln, Kreativ Selbst Gestalten, Deko Kinderdeko Dekoration, Spaß & unzäglige Möglichkeiten : Amazon.de: Handmade Produkte

Fingerstempelbuch für Kinder ab 2 Jahre: Bauernhof Tiere Punktmarker Malbuch und Bastelbuch | 40 Fingerabdruck Motive zum kreativen Malen und Basteln ... | Nutztiere Finger-Malspaß : Wollenburg, Susan Petra: Amazon.de: Bücher

Kita-to-Go: Mit Leoli auf dem Bauernhof – Das Mitmachbuch – Spielen, Basteln, Bewegen, Lernen: Vielseitiges Mitmachbuch für Kindergartenkinder ab 3 (Die Kita-to-Go-Serie, Band 3) : Puttich, Marie-Luisa, Puttich, Marie-Luisa: Amazon.de: Bücher

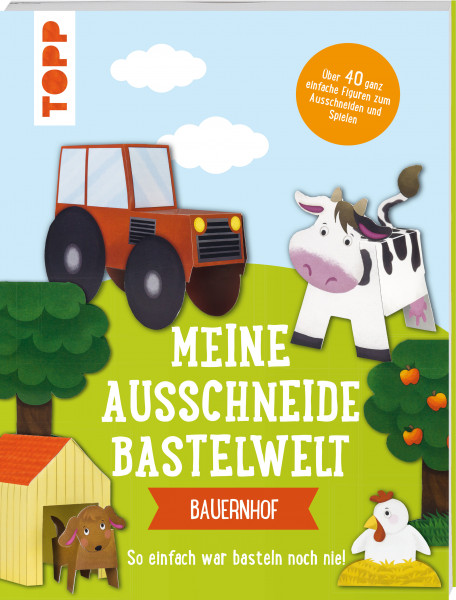
Das Ausschneide-Bastelbuch – Arche Noah: Tolle Figuren zum Basteln und Spielen, ganz einfach und kinderleicht mit Stift, Schere und Klebstoff : Küssner-Neubert, Andrea: Amazon.de: Bücher

ATELIER COLOR Bauernhof Bastelbogen mit Tieren für Kinder zum Basteln ab 5+ Jahren Spielzeug aus Papier Bastelset Papiermodelle zum Spielen: Amazon.de: Spielzeug

ATELIER COLOR Bauernhof Bastelbogen mit Tieren für Kinder zum Basteln ab 5+ Jahren Spielzeug aus Papier Bastelset Papiermodelle zum Spielen: Amazon.de: Spielzeug

Holz Tiere Bauernhof 16-teilig, Bauernhoftiere zum Bemalen, Basteln, Kreativ Selbst Gestalten, Deko Kinderdeko Dekoration, Spaß & unzäglige Möglichkeiten : Amazon.de: Handmade Produkte

Filz Basteln für Kinder Filzdekoration Bauernhof-thema Filzplatte Filzmatte Filz zum Basteln Filzstoff Bastelfilz Basteln Mädchen 8 Jahre : Amazon.de: Spielzeug

Filz Basteln für Kinder Filzdekoration Bauernhof-thema Filzplatte Filzmatte Filz zum Basteln Filzstoff Bastelfilz Basteln Mädchen 8 Jahre : Amazon.de: Spielzeug

Wieso? Weshalb? Warum? aktiv-Heft: Bauernhof: Malen, Rätseln, Basteln. Mit Stickern und Bastelbogen : Merle, Katrin: Amazon.de: Bücher